Transparent Proxying
Transparent Proxying is the ability of a proxy (such as ATS) to intercept connections between clients and servers without being visible.
The general network structure that will be used in this documentation is shown in the following figure.
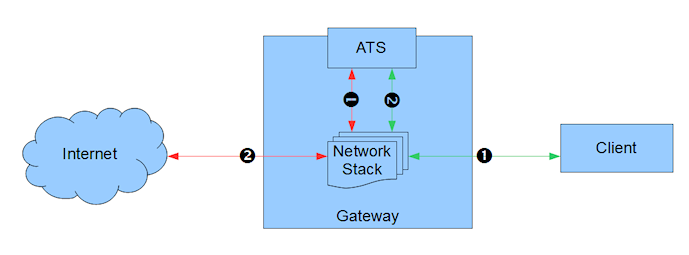
ATS basic traffic flow of Transparent Proxy
There must be a gateway device through which all network traffic passes from the client to the Internet (or external cloud). The gateway is responsible for effectively splicing ATS in to selected streams of that traffic. Each traffic stream is split in two, with ATS terminating both sides. That is, stream green-1, red-2, is split in to the green connection and the red connection. Note that ATS may or may not be on the gateway system, the redirected traffic can flow over other network infrastructure.
Because ATS uses two connections, transparency can be set independently on the client and origin server (Internet / external cloud) side. We will define what is generally called “transparent proxy” as two aspects, inbound transparency and outbound transparency.
Inbound transparency is a proxy that is transparent to connections that are inbound to the proxy, i.e. a connection initiated by a client which connects to the proxy (green-1). Similarly, outbound transparency is a proxy that is transparent to connections that are outbound from the proxy, i.e. a connection initiated by the proxy to an origin server (red-2).
In most situations these two types of transparency are combined, but that is not required. Traffic Server supports transparency independently on the two sides.
Important
It is critical to note that any transparency requires specialized routing and cannot be done solely by configuring ATS. ATS transparency also requires support from the Linux kernel and therefore currently only works on sufficiently recent Linux kernels that support the following features:
TPROXY
POSIX capabilities
In addition the specialized routing will require using iptables and
in some cases ebtables.
Standard build procedures should work for transparency support but if not consult these more detailed instructions.
Transparency is configured per server port, not globally. This is done
via the configuration values proxy.config.http.server_ports, specifically tr-in, tr-full, and tr-out.
In the outbound transparent case clients must connect directly to ATS either through an explicit proxy mechanism or by advertising the IP address of the ATS server via DNS as the origin server address.
The proxy.config.http.use_client_target_addr should also be reviewed when setting up an outbound
transparent scenario. If Traffic Server has the same DNS as the client, options 1 and 2 can be used. Otherwise,
option 2 must be used.
Some tested scenarios –